Cybersecurity: Part 1 — Demystifying Cyberthreats*
by Qing Liu, Technology Architect, and Sebastiaan Gybels, Risk Management Team Leader, Federal Reserve Bank of Chicago
The U.S. Department of Defense revealed that "at the top of the U.S. intelligence community's 2013 assessment of global threats is cyber, followed by terrorism and transnational organized crime."1 The severity and impact of cyberthreats have changed the landscape in which governments, corporations, individuals, and, specifically, financial institutions of all sizes and complexities operate.
This article, which is the first of a two-part series, provides background information on cyberthreats and helps individuals working in financial institutions to better understand cyber-related risks and exposures.
What Are Cyberthreats?
According to the U.S. Department of Homeland Security, cyberthreats refer to the possibility of or attempt of gaining unauthorized "access to a device or system or network using a data communication pathway."2 Seven of the most common cyberthreats or cyber-related risks that community banks have identified and experienced include the following:
- Malicious software, or "malware"
- Distributed denial of service attacks
- Automated clearinghouse (ACH)/payment account takeover
- Data leakage
- Third-party/cloud vendor risks
- Mobile/web application vulnerabilities
- Weaknesses in project management or change management
Who Are the Culprits Behind Cyberthreats?
Cyberthreats can come from numerous sources. The U.S. intelligence community has identified several culprits who are responsible for deliberate cyberthreats, including criminal groups, foreign intelligence services, hackers, insiders, and terrorists. It is important to note that these malicious acts are not only perpetrated by external attackers; in some cases, attacks have originated from employees inside a financial institution.
How Do Cyberattacks Affect Community Banks?
Before the digital age, when somebody robbed a bank, the pool of suspects was "limited to the number of people in the general vicinity of that bank," according to Shawn Henry, the former executive assistant director of the FBI's Criminal, Cyber, Response, and Services Branch.3 "Today when a bank is robbed digitally … the pool of suspects is limited to the number of people on the face of the earth that have a laptop and an Internet connection, because anybody with an Internet connection potentially can attack any other computer that's tied to the network. So the barrier of entry is relatively low."
Financial institutions not only suffer direct financial losses due to cyberattacks but they also face enormous costs when they are victimized by large-scale data breaches following these attacks. These costs include but are not limited to:
- Investigation and forensic costs
- Customer and partner communications costs
- Public relations costs
- Lost revenue due to a damaged reputation
- Regulatory fines
- Civil claims and legal fees
In the Ponemon Institute's 2013 Cost of Cyber Crime Study,4 the median annualized cost of cybercrime in the study's benchmark sample was $9.1 million — an increase from the previous year's median cost of $6.2 million. Not having adequate protection against cybercrimes poses a huge operational risk and potentially places a great financial burden on a community bank.
What Are Cyberthreats and Cyber-Related Risks?
Clearly understanding cyberthreats and their mechanisms is the first step in evaluating the risk exposures to financial institutions. Following is a discussion of seven of the most common cyberthreats and cyber-related risks.
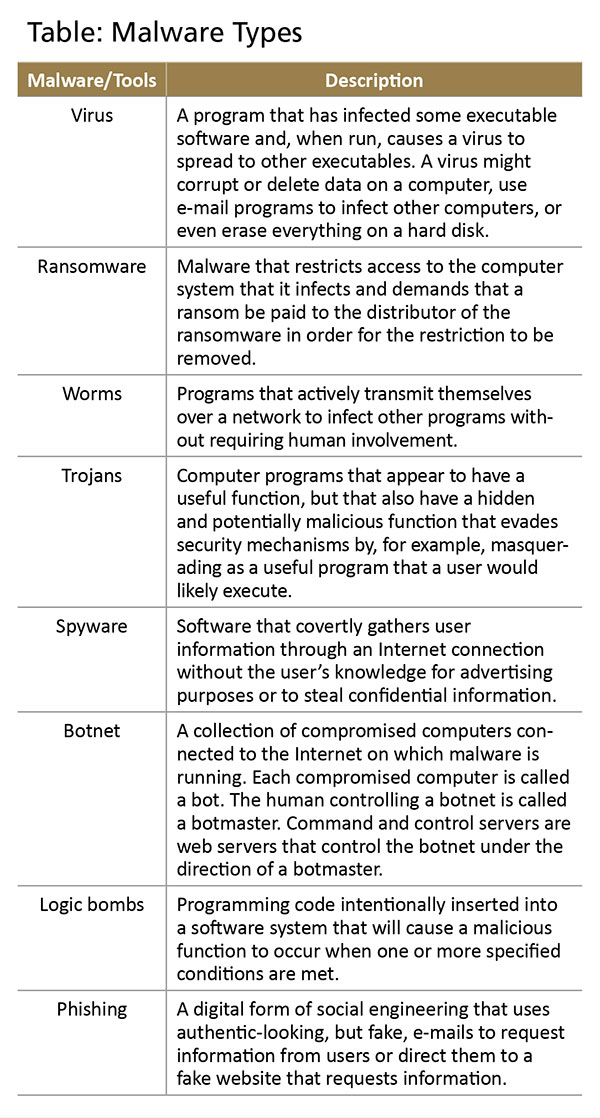
Malware is software that is used to disrupt computer operations, gather sensitive information, or gain access to private computer systems. Malware operates by breaching a bank's network, seeking out weaknesses and points of attack — even in the presence of security controls. Malware infections can occur via physical media, such as USB memory sticks, CDs and DVDs, memory cards, and appliances, or through Internet media, such as drive-by downloads, e-mail attachments, file sharing, pirated software, and phishing. Types of malware include computer viruses, ransomware, worms, Trojans, keyloggers, spyware, adware, botnet, and logic bombs, among others; more information about many of these various forms is provided in the table.5
Distributed denial of service (DDoS) attacks, which have been used extensively since 2012, repeatedly target major U.S. banking websites and services, making the institutions' online services unavailable. The wave of DDoS attacks has a broad range of targets, including large regional and community banks as well as credit unions and technology service providers.
DDoS attacks occur when an attacker leverages a number of computers from various locations to send simultaneous requests to a target computer or website. In other words, the attack has the same effect as if millions of users were simultaneously opening a web browser and going to the same web page. The overwhelming flood of requests to the web server or computer network is intended to cause a shutdown or failure to handle the requests of legitimate users, much like a rush-hour traffic jam on a freeway. The goal of a DDoS attack is usually to limit, disrupt, or prevent access to a particular network resource or web service. Although these attacks pose limited financial risk, they clearly create reputational risks for the affected banks, since their customers may experience a slower-than-usual connection or be unable to access online banking services.
ACH/payment corporate account takeover is a type of identity theft in which cyberthieves gain control of a business's bank account by stealing the business's valid online banking credentials through various methods. A classic example of this type of cybercrime was an ACH/account takeover at a community bank. To initiate the attack, several e-mails from an industry group were circulated to an employee of one of the bank's commercial customers. The e-mail stated that a transaction had not cleared properly and that the reader should click on a link to resolve the problem. As soon as the e-mail link was clicked, hackers were able to install a keylogger — a program that tracks a user's activity and allows access to the commercial customer's bank accounts. After gaining the commercial customer's online banking passwords, the perpetrators directed the bank to process a money transfer to an offshore account. The commercial customer received a confirmation of the transaction and immediately called the bank to stop it, but it was too late — the money was gone.
Data leakage is the unauthorized transmission of data or information from within an organization to an external destination or recipient. This can be executed electronically or through a physical method. The data leakage can be intentional and malicious, or unintentional and inadvertent.
According to the SANS Institute, data leakage is categorized into four types: the most common is customer data, at 73 percent; then confidential information, at 15 percent; and finally intellectual property and health records, each at 8 percent.6 Of all data leakage incidents, 52 percent are from internal sources, compared with the remaining 48 percent by external hackers. Internal data leakage is significant because it is mainly caused by a lack of employee oversight and weak business processes. Internal data leakage may occur through various communication channels such as instant messaging, e-mail, web mail, web logs/wikis, malicious web pages, removable media/storage devices, hard copy, cameras, and unsafe file transfer protocols, among other methods. External data leakage is mainly triggered by external hackers using social engineering or malware, phishing, or taking advantage of web application vulnerabilities.
Third-party/cloud vendor risks will expose a financial institution to risks that are outside of its immediate control; therefore, the financial institution has to rely on due diligence in the contract and monitoring of the service provided, rather than being able to manage the risk in-house. Third-party/cloud vendors provide critical services to financial institutions such as core data processing, payment processing, credit card processing, mobile banking, and ensuring business continuity. Banks' sensitive data are often handled or stored by third-party vendors and their subcontracted companies for business purposes. When a data breach occurs at these vendors, it can directly jeopardize the confidentiality, integrity, and availability of the financial institution's data. It is important to note that a bank can outsource operational functions to third parties, but the bank will remain the owner of bank data and, therefore, is ultimately responsible. Additionally, when a cyberattack targets a service provider, the attack might not be directed at a specific financial institution. This means that whenever the cyberattack affects the service provider's environment, it may impact the operations of several banks that are using the same operating environment. Therefore, the concentration of services by third-party vendors can negatively impact multiple banks even when the affected banks are not the direct targets of a cyberattack.
Mobile/web application vulnerabilities are the weaknesses or flaws that reside in a mobile application, smartphone, or Internet-facing web server. To expand business and attract new customers, more financial institutions are leveraging innovative technology, such as mobile payment applications on smartphones or tablets.7 The mobile platform (both smartphone and mobile applications) is still maturing, and it does not always provide the same level of security features that are typically found on a desktop or laptop. As a result, a hacker can use tools to gain access to and exploit the mobile platform, gain sensitive information stored or processed by mobile applications on the customer's mobile device, or take over controls of a payment web server.
Weaknesses in project management or change management can directly expose a bank's core financial systems or sensitive data. Banks use project management and change management to address changes in the information technology infrastructure to support current business processes or integrate new technology or products. Banks also have change management processes in place to update existing systems or products, patch the vulnerabilities in legacy products, and manage the life cycle of software and hardware. Weaknesses in project management or change management processes can undermine policies and procedures, delay vulnerability discovery and mitigation, and expose bank systems or sensitive data to intruders.
Conclusion
Cyberthreats and cyberattacks have increased dramatically over the past several years. They have exposed sensitive personal and business information, disrupted the critical operations of institutions, and imposed high costs on the economy and business operations. That is why it is imperative that financial institutions stay informed about the continuously changing forms of cyberthreats and develop appropriate, cost-effective controls to safeguard their businesses. Part two of this article will expound upon the four control pillars of a general cybersecurity framework: risk assessment; policy, procedure, and control implementation; governance and monitoring; and resiliency and incident response.
Back to top
- * This article focuses on the seven most significant cyberthreats or risks currently encountered throughout the financial system. A second article will discuss a risk management framework that can be used to implement controls and evaluate the effectiveness of the cybersecurity measures in both financial institutions and associated third-party vendors.
-
1
Cheryl Pellerin, "Cyber Tops Intel Community's 2013 Global Threat Assessment," U.S. Department of Defense, April 15, 2013, available at
www.defense.gov/News/newsarticle.aspx?ID=119776
 .
.
-
2
Industrial Control Systems Cyber Emergency Response Team, "Cyber Threat Source Description," available at
http://ics-cert.us-cert.gov/content/cyber-threat-source-descriptions
 .
.
-
3
Federal Bureau of Investigation, "FBI's Top Cyber Official Discusses Threat," available at
www.fbi.gov/news/videos/fbis-top-cyber-official-discusses-threat
 .
.
-
4
Ponemon Institute, 2013 Cost of Cyber Crime Study: United States, available at
media.scmagazine.com/documents/54/2013_us_ccc_report_final_6-1_13455.pdf
 .
.
- 5 Nader Mehravari, "Cybersecurity Update," CERT Cyber Resilience Center, Carnegie Mellon University, July 16, 2013.
-
6
Peter Gordon, SANS Institute, Data Leakage — Threats and Mitigation (2007), available at
www.sans.org/reading-room/whitepapers/awareness/data-leakage-threats-mitigation-1931?show=data-leakage-threats-mitigation-1931&cat=awareness
 .
.
- 7 For more information about the risks involved with mobile banking and how to mitigate those risks, see Jerome F. Combs, "Mobile Banking Risk Identification and Mitigation," Community Banking Connections, First Quarter 2014.
