Denver Cybersecurity Conference Reminds Bankers to Be Vigilant
by Brian Brown, Senior Examiner, Federal Reserve Bank of Kansas City
The 2nd Annual Denver Cybersecurity Conference, featuring presentations from federal law enforcement agents, bank officers, and bank regulatory professionals, took place at the Denver Branch of the Federal Reserve Bank of Kansas City on December 14, 2016. The conference was cosponsored by the Federal Reserve Bank of Kansas City, the Federal Bureau of Investigation (FBI), the U.S. Secret Service, the Office of the Comptroller of the Currency, the Federal Deposit Insurance Corporation, and the Colorado Division of Banking. More than 60 bankers and regulators attended the conference.
The conference presenters shared their real-world cybersecurity experiences with attendees. They discussed how current cybersecurity risks are escalating and made recommendations for preventing and responding to these risks. The consensus was that cybersecurity threats continue to pose increased risks that require the collective efforts of bankers, law enforcement agents, and regulators to effectively combat the danger to the banking industry.
The law enforcement panel opened the conference and confirmed that cybersecurity risks remain a top threat to businesses and the government. The federal law enforcement representatives explained that criminal actors, a majority of whom are located outside of the United States, are stealing funds by executing various types of financial fraud schemes. The presenters gave attendees an overview of the different types of cyber-related fraud being perpetrated and provided information on how to effectively deal with these issues.
Topics Discussed During the Conference
In the first session, the panel provided information about e-mail spoofing, the Financial Fraud Kill Chain, and ransomware. The second session included a panel of bank professionals who discussed cybersecurity threats identified during their day-to-day operations. The panelists shared examples of internal and external threats along with the best practices for remediation. The final session of the conference included a panel of representatives from bank regulatory agencies. The panelists summarized current examination findings and answered participants’ questions.
The following topics were discussed as the various experts shared their thoughts and concerns.
Wire Fraud
All three panels addressed the subject of wire fraud. Various panelists pointed out that criminals will use a spoofed e-mail1 to obtain customer information or to take over the e-mail accounts of customers or bank executives. Once criminals have the customer’s information or have compromised an e-mail account, they can originate fake wire transfer requests or initiate other types of money transfers from the bank. These fraudulent transactions often occur on a Friday afternoon to instill a sense of urgency and to limit the bank’s ability to recover the fraudulent wire transfer. As soon as wire fraud is suspected, the bank should follow its usual procedures for recalling the fraudulent funds, which involve quickly notifying the receiving bank.
Law enforcement agents who were on the panel indicated that they can help bankers attempt to recover large international wire transfers by using the Financial Fraud Kill Chain (FFKC).2 The FFKC can be initiated if the victim is located in the United States, the fraudulent wire transfer is international, the transfer is greater than or equal to $50,000, the transfer has occurred within the past 72 hours, and a recall notice3 has been issued by the Society for Worldwide Interbank Financial Telecommunication (SWIFT). U.S. law enforcement agents use their relationships with law enforcement agents in other countries to help recover illegally obtained funds. Although not all countries cooperate with U.S. law enforcement agents, the panelists indicated the success rate was fairly good.
Conference participants also expressed concern about the lack of adequate controls over wire transfers. Panelists recommended that written procedures specify the processing protocol for incoming and outgoing wire transfers, the protocol for posting and balancing entry procedures, and employees’ responsibilities for implementing these policies. The processing of wire transfers should be performed under dual control, and the bank staff who are allowed to send or approve wires should have preset approval limits. Customers who frequently request wire transfers should be required to sign wire transfer agreements, and callback procedures should be established for wire transfers over a certain dollar threshold.4
Ransomware
The law enforcement panel indicated that the number of victims and the dollar volume of losses caused by ransomware continue to increase. Criminals use ransomware to encrypt data on an infected computer until the user pays a ransom to the originator of the malware. After the ransom is paid, the originator may or may not give the user a key to unlock the information. More than 200 variations of ransomware are currently estimated to exist, and cybercriminals are constantly developing new versions. The FBI has seen 35 to 38 new variants in as few as two months. The FBI also estimated that only about one-third of ransomware victims report the crime to law enforcement. The reasons for not reporting these crimes are varied but seem centered around reputational risk. The figure below details the stages of ransomware.
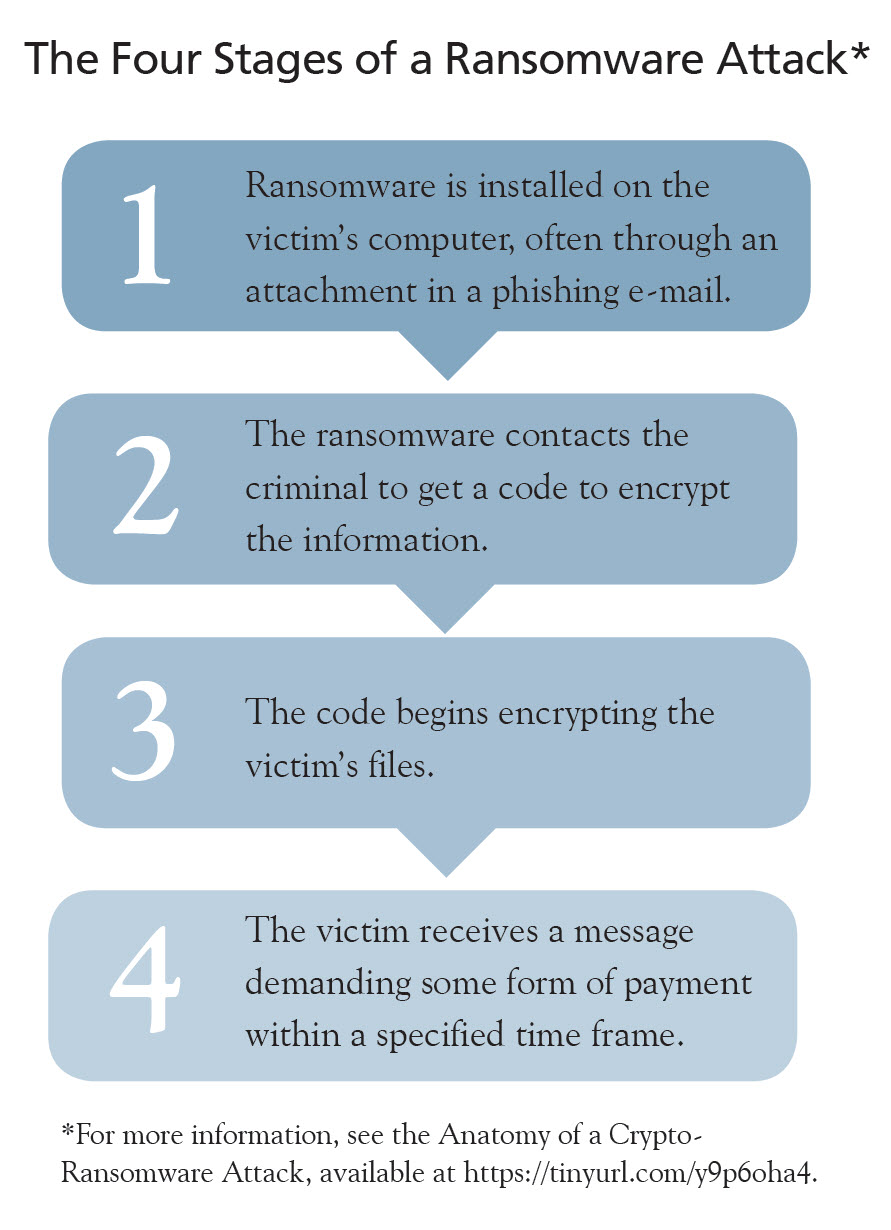
To hide the origin of the e-mail that delivered the ransomware, criminals use a process called onion routing.5 The criminal typically asks for the payment to be made in some form of electronic currency so that it is difficult to track the funds. Ransomware has various names, including CryptoWall, CTB Locker, TeslaCrypt, MSIL/Samas.A, and Locky. While the most prevalent victims are hospitals and government networks, banks are also targeted.
Bank management can protect their institutions from ransomware by:
- focusing on staff awareness and training;
- regularly updating software patches;
- automatically updating antivirus and malware software;
- managing privileged administrator accounts;
- implementing the principle of least privilege (giving bank staff the minimal level of access that they need to perform their jobs);
- having robust backup and restore procedures; and
- implementing software installation restriction policies.
Federal law enforcement does not condone paying the ransom because it encourages criminals and funds illegal activity.
Phishing
One of the banker panelists estimated that approximately 91 percent of cyberattacks originate through phishing e-mails and other methods of social engineering. Bankers were encouraged to conduct vulnerability and social engineering tests on a regular basis to reduce the chances of employees unknowingly clicking on an infected e-mail. Employees subject to the test should not know when a social engineering test is going to be conducted to avoid skewing the test results.
Friendly Fraud
Another banker panelist estimated that 70 percent to 80 percent of credit card fraud is the result of “friendly fraud.” Friendly fraud occurs when a product is purchased from an online store, but after the customer receives the product, he or she tells the credit card company to reverse the charge because the merchandise wasn’t received. The card issuer, such as VISA or MasterCard, will then cancel the transaction and give the person who initiated the purchase his or her money back. In the end, the consumer obtains a refund from the credit card company but also keeps the product. Ultimately, the loss has to be absorbed by either the bank or the merchant.6
Printed Documents
The banking panel reminded attendees that printed documents with sensitive or confidential customer information (for example, a customer’s loan file or credit card application) are difficult to secure because they can be easily misplaced. Both bank staff and customers were encouraged not to print documents unless absolutely necessary. A significant problem noted with regard to printed material is that organizations do not know if a printed document has been lost.
Internet of Things
Bankers reminded attendees that the Internet of Things (IoT) poses new threats. The IoT refers to mechanical devices connected to the Internet, such as video cameras and home thermostats.7 If not adequately secured and protected, these Internet-connected devices can expose organizations and individuals to security risks. One panelist gave an example of a security camera that, when connected to the network, immediately started attempting to send messages to China. Bank management should monitor devices that seem harmless, such as photocopiers, because the information accessed or stored on these devices can possibly be compromised.
Anomaly Detection
The banker panel indicated that banks have the ability to observe customers’ normal patterns of performing transactions and, based on these data, are able to develop a baseline of customers’ behavior. This baseline helps banks to more quickly identify behavioral anomalies that may indicate incidents of fraud. Banks can use anomaly detection software to help create and monitor baseline behavioral patterns. Incident response program flow charts detailing the steps the bank will take during a cybersecurity event should also be developed and regularly tested.
Employee Training
Employees who are trained to identify fraud are a bank’s greatest resource. The conference participants agreed that, to promote the effectiveness of training, banks need to make fraud detection training fun and competitive to keep employees engaged. One-time training events were seen to effectively change behavior for only two to three months; therefore, regularly repeating the training was encouraged. Employees need to feel that they are part of the solution.
Threat Intelligence
The bank’s cybersecurity experts should monitor threat intelligence and should provide related information to the bank’s board of directors, staff, and customers when appropriate. Banks should discern between minor and significant threats and should educate bank staff and customers about these threats so that they can be readily identified and reported to management.
Data Leakage
Data leakage occurs when unauthorized parties obtain sensitive data through either malicious intent or an inadvertent mistake by an employee. Panelists recommended various steps to assist with data loss prevention, including shutting off USB ports and filtering out the content of outgoing messages. Shutting off USB ports prevents the downloading of sensitive or confidential information to USB flash memory sticks. Filtering content out of outgoing messages can be done through a program that screens outgoing e-mails for sensitive information and prevents the sending of an e-mail with sensitive information.
User Groups
Banks’ information technology and cybersecurity experts were encouraged to be involved in the user groups of critical software vendors. User group meetings offer an opportunity for software users to discuss their cybersecurity concerns and to share those concerns with the vendor.
User Access Levels
Management should closely monitor user access levels to ensure bank employees have no more access rights to information and systems than required to do their jobs. This is known as the principle of least privilege. For example, a bank’s senior management should not have administrative access to critical systems because these individuals are often targeted by hackers. If a bank senior officer has administrative access and that access is stolen, the hackers will be able to make unrestricted, potentially adverse, system-wide changes to the bank’s critical systems.
A Bank’s Board of Directors
While not a regulatory requirement, conference panelists suggested that a bank’s board of directors take time to discuss cybersecurity issues at every board meeting and seek to understand the issues. Discussions should cover topics such as the different types of cybersecurity breaches and the potential harm of such breaches to the bank; the board’s role in overseeing cybersecurity and providing risk oversight; the importance of having a cybersecurity framework for the bank; the bank’s efforts to prepare for cybersecurity incidents; and measures to take to prevent an incident as well as possible responses to a breach.
Conclusions
The general consensus of the conference participants is that banks need to take measures to improve the protection of their information and systems. In addition to establishing processes to identify and manage cyberthreats, as discussed in this article, bankers should also (1) maintain an inventory of their information technology assets and systems, (2) develop a program for promoting customer awareness about how to protect personal and bank information, (3) develop processes for monitoring critical third-party interconnectedness and resilience plans, and (4) maintain and periodically test an incident response plan to address cybersecurity breaches as well as testing of the plan.8
Back to top- 1 In e-mail spoofing, the header of the e-mail has been manipulated to make the message look as if it is being sent from a legitimate source or from a source other than the sender.
- 2 See Federal Bureau of Investigation, Financial Fraud Kill Chain, January 11, 2016, available at
https://tinyurl.com/y8dxwrno
 .
. - 3 Recall notices are initiated by the sending bank when it wants to recall a wire. The wire can sometimes be canceled, depending on the time it was received. The receiving bank has to obtain the recall notice before the money is withdrawn from the account into which the wire funds were deposited. The receiving bank can only send the money back if it has not been withdrawn by the perpetrator. See Independent Bankers Bank Association of Texas, Operations, Wire Transfer: Recall of Wire by Originator, available at
https://tinyurl.com/y7ypmbk9
 .
. - 4 Community Banking Connections published an article titled “Managing the Risk of Unauthorized Payments from Business Bank Accounts” in the Second Quarter 2015 issue that discusses ways to mitigate the risk of wire fraud. This article is available at www.cbcfrs.org/articles/2015/q2/managing-the-risk-of-unauthorized-payments.
- 5 Onion routing simply means that messages with several layers of encryption, like the layers of an onion, are anonymously routed. For more information about onion routing, see Marc O’Morain, Vladislav Titov, and Wendy Verbuggen, “Onion Routing for Anonymous Communications,” available at
https://tinyurl.com/ybcyvllu
 .
. - 6 See David Lott, "Friendly Fraud: Nothing to Smile About (Part 1),"
Federal Reserve Bank of Atlanta, 2015, available at
http://takeonpayments.frbatlanta.org/2015/07/friendly-fraud-nothing-to-smile-about-part-1.html.

- 7 See Jacob Morgan, "A Simple Explanation of 'The Internet of Things,'"
Forbes, May 13, 2014, available at
https://tinyurl.com/yabtdfzv.

- 8 The FFIEC IT Exam Handbook InfoBase, which is available at
http://ithandbook.ffiec.gov/it-booklets.aspx,
 provides additional
information. See also Brian Bettle, "Less Risky Business: An Overview of a
New Cybersecurity Assessment Tool," Community Banking Connections, Second
Issue 2016, available at
www.cbcfrs.org/articles/2016/i2/less-risky-business, and Qing Liu and
Sebastiaan Gybels, "Cybersecurity: Part 2 — Cyber-Related Assessment and
Controls," Community Banking Connections, Third/Fourth Quarter 2014,
available at
www.cbcfrs.org/articles/2014/q3-q4/cybersecurity-part-two.
provides additional
information. See also Brian Bettle, "Less Risky Business: An Overview of a
New Cybersecurity Assessment Tool," Community Banking Connections, Second
Issue 2016, available at
www.cbcfrs.org/articles/2016/i2/less-risky-business, and Qing Liu and
Sebastiaan Gybels, "Cybersecurity: Part 2 — Cyber-Related Assessment and
Controls," Community Banking Connections, Third/Fourth Quarter 2014,
available at
www.cbcfrs.org/articles/2014/q3-q4/cybersecurity-part-two.
